Context
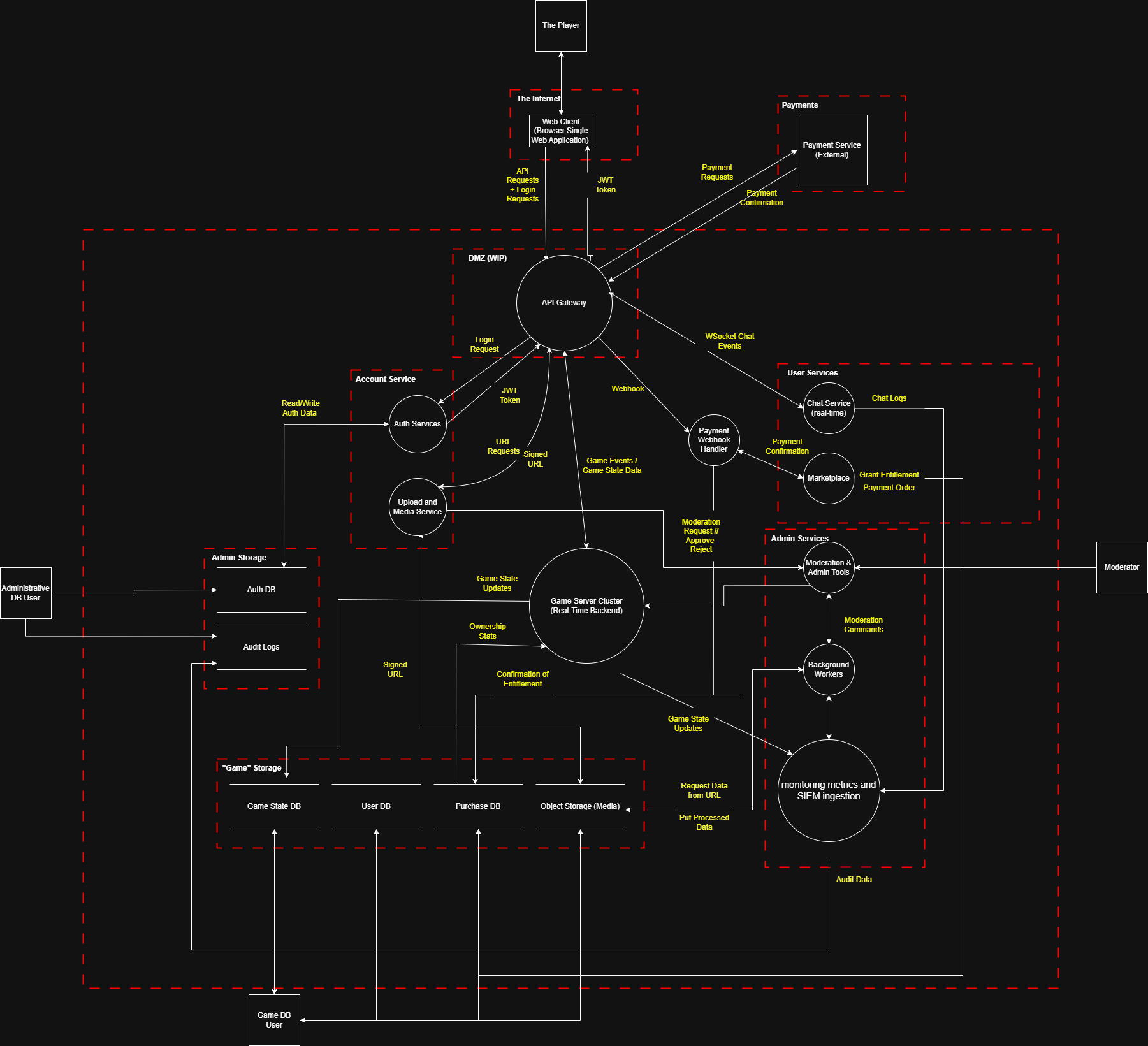
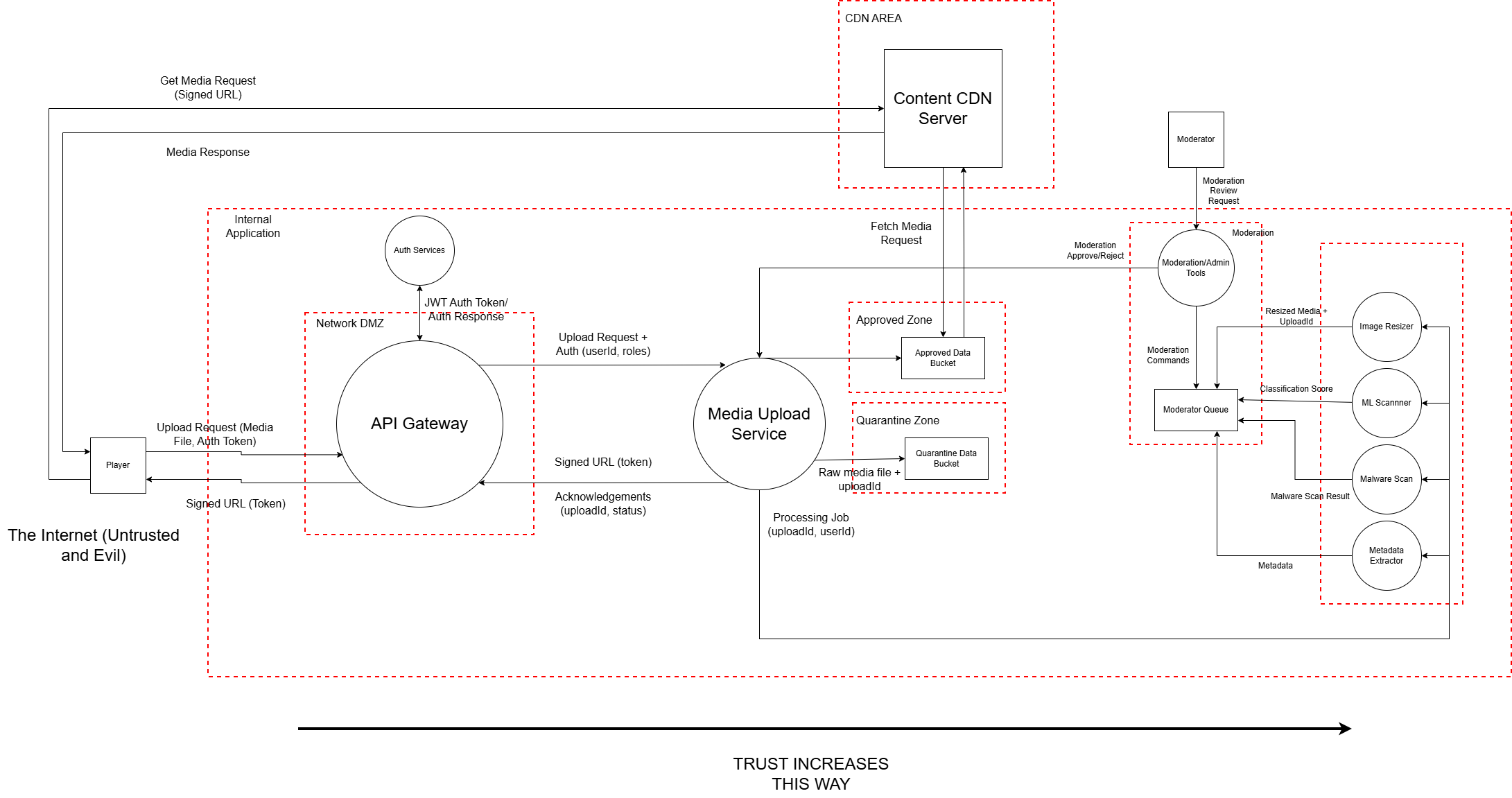
We performed threat modelling on an online multiplayer city-building game and focused on three key areas for in-depth analysis.
Interactive report covering authentication, media uploads, and payment systems.
Context, executive summary, objective, scope, and assumptions.
We performed threat modelling on an online multiplayer city-building game and focused on three key areas for in-depth analysis.
We focused on three high-impact areas: authentication, media uploads, and payment/marketplace. Key risks center around financial loss, abuse of external callbacks, and integrity of user assets and transactions.
This threat modelling exercise identifies risks in the game's system, assesses their business impact, and provides recommendations for mitigation. Our priorities are:
| Assumption | Reason | Security Impact | How to Validate |
|---|
This threat modeling exercise supports our business continuity and risk management goals. By addressing threats to authentication, media uploads, and payments, we can:
General DFD + component DFDs (Auth, Media Upload, Payment).
We selected these areas based on their business impact and attack surface.
Click a cell to highlight threats in that band.
Click components on the DFD to reveal details.
Filter the table; click a threat to see details + mitigations.
| ID | Subsystem | Components Affected | Data Asset | Data Flow | S | T | R | I | D | E | Threat Name | Threat Description | Possible Impact | Likelihood Score | Impact Score |
|---|
Browse by subsystem, analyse controls, or view mitigation coverage & ROI.
Click a threat to view mitigations